How To Enable Tls 1.2 On Windows Server 2008 R2
Showtime published on MSDN on Jan 29, 2016
Microsoft is pleased to announce the release of (Send Layer Security) TLS 1.2 support in all major client drivers and SQL Server releases. The updates fabricated available on January 29th, 2016 provide TLS 1.2 back up for SQL Server 2008, SQL Server 2008 R2, SQL Server 2012 and SQL Server 2014 . The client drivers that have support for TLS 1.2 are SQL Server Native Customer , Microsoft ODBC Commuter for SQL Server , Microsoft JDBC Driver for SQL Server and ADO.NET (SqlClient) .
The list of SQL Server server and client component updates along with their download locations that support TLS 1.two is available in the KB Article below:
3135244 TLS ane.2 support for Microsoft SQL Server
You can use KB3135244 to download the advisable server and client component applicable for your surround. The first build numbers that provides complete TLS one.2 support in each major release is available in KB3135244 equally well. The post-obit tables lists the client driver/components and server components which have TLS 1.2 support. You will need to apply the necessary client component fixes on the server that hosts the SQL Server case (eg. MS ODBC Driver, SQL Server Native Client) to ensure that the client components installed on the server as well back up TLS ane.2.
| Client Components | Server Components |
| SqlClient (.NET Framework four.6) | SQL Server 2014 |
| SqlClient (.Net Framework 4.5.two, 4.v.i, 4.five) | SQL Server 2012 |
| SqlClient (.Cyberspace Framework four.0) | SQL Server 2008 R2 |
| SqlClient (.Cyberspace Framework 3.5/a.one thousand.a (.Net Framework 2.0 SP2) | SQL Server 2008 |
| MS ODBC Driver v11 (Windows) | |
| SQL Server Native Client (for SQL Server 2012 & 2014) | |
| SQL Server Native Client (for SQL Server 2008 R2) | |
| SQL Server Native Client (for SQL Server 2008) | |
| SQL Server Native Client (for SQL Server 2005) | |
| JDBC half dozen.0 | |
| JDBC four.2 | |
| JDBC iv.1 | |
You can use the PowerShell script from our tigertoolbox GitHub repository to determine which client drivers on your server and customer machines require fixes.
Update: March ii, 2016 : Please encounter known issue half-dozen for the intermittent service terminations that were reported after installing the update.
Update May 27, 2016 : Additional fixes needed for SQL Server to employ TLS 1.two with Database Mail is available at KB3135244 .
Update January 31, 2017: If you lot want to check if the TLS/SSL protocol that is being used by the client connection, then you lot can use the TRACE extended outcome (nether DEBUG channel) to make up one's mind the TLS/SSL protocol, zippo, hash and peer address for the connection being made. This capability is available in SQL Server 2016 Service Pack one and above. Run across KB3191296 for more details.
Consequence 1
SQL Server Management Studio (SSMS), Written report Server, and Report Director don't connect to the database engine afterwards you apply the fix for SQL Server 2008, 2008 R2, 2012, or 2014. Report Server and Report Managing director fail and return the following error message:
The written report server cannot open a connection to the report server database. A connection to the database is required for all requests and processing. (rsReportServerDatabaseUnavailable)
This issue occurs because SSMS, Study Manager, and Reporting Services Configuration Director employ ADO.Net, and ADO.Net support for TLS 1.2 is available only in the .Cyberspace Framework 4.6. For earlier versions of the .Internet Framework, you lot have to use a Windows update and so that ADO.Internet can support TLS 1.two communications for the client. The Windows updates that enable TLS ane.two support in earlier versions of .Internet framework are listed in the table in the "How to know whether you need this update" section of KB3135244.
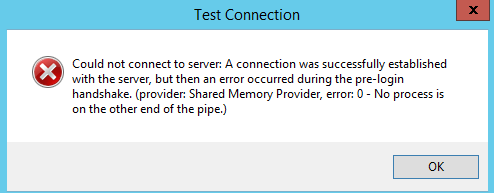
Issue 2: Reporting Services fails to start
Reporting Services Configuration Managing director reports the following fault bulletin fifty-fifty afterwards customer providers have been updated to a version that supports TLS i.ii:
Could not connect to server: A connectedness was successfully established to the server, simply then an error occurred during the pre-login handshake.
To resolve this problem, manually create the following registry key on the system that hosts the Reporting Services Configuration Manager:
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.ii\Customer : REG_DWORD=Enabled, "Enabled"=dword:00000001
Issue 3: Encrypted endpoint advice fails
The encrypted endpoint communication that uses TLS ane.2 fails when yous employ encrypted communications for Availability Groups or Database Mirroring or Service Banker in SQL Server. An error message that resembles the following is logged in the SQL Error log:
Connection handshake failed. An Os call failed: (80090331) 0x80090331(The customer and server cannot communicate, because they do not possess a common algorithm.). Country 56.
For more information about this effect, run into Set: The encrypted endpoint communication with TLS 1.2 fails when yous utilise SQL Server .
(Update: February 22, 2016) Known Issue: If yous are on a currently using Cumulative Update for SQL Server 2014 and demand to use TLS 1.2 for encrypted endpoints for features like Availability Groups, Database Mirroring or Service Broker, and so nosotros recommend that you install Cumulative Update 1 for SQL Server 2014 Service Pack 1 or Cumulative Update 8 for SQL Server 2014 which adds support for this particular scenario. This is documented as a known event in KB3135852 .
Result 4: Encrypted communication with DBM/AG fails
An encrypted connection with Database Mirroring or Availability Groups does non work when y'all apply a certificate after you disable all other protocols other than TLS one.2. An mistake message that resembles the following is logged in the SQL Server Fault log:
Connection handshake failed. An OS phone call failed: (80090331) 0x80090331(The client and server cannot communicate, considering they do not possess a common algorithm.). State 58.
There might exist additional errors that yous might encounter in the upshot logs associated with this issue as shown below.
Log Name: System Source: Schannel Date: 3/4/2016 2:09:28 AM Effect ID: 36888 Task Category: None Level: Fault Keywords: User: System Description: A fatal alarm was generated and sent to the remote endpoint. This may outcome in termination of the connectedness. The TLS protocol defined fatal error code is 40. The Windows SChannel fault state is 1205.
Log Name: Organization Source: Schannel Date: 3/4/2016 two:09:28 AM Consequence ID: 36874 Task Category: None Level: Error Keywords: User: SYSTEM Clarification: An TLS 1.2 connection request was received from a remote client application, but none of the cipher suites supported by the client application are supported by the server. The SSL connection request has failed.
Issue 5 : SQL Server Setup fails
SQL Server setup fails when TLS 1.2 is enabled
When you lot try to install Microsoft SQL Server 2012 or SQL Server 2014 on a server that has Transport Layer Security (TLS) version 1.2 enabled, you may encounter the following issues:
- If the version of SQL Server that you're trying to install doesn't contain the fix to enable TLS 1.2 back up, y'all receive the post-obit mistake bulletin:Wait on the Database Engine recovery handle failed. Check the SQL Server error log for potential causes.
- If the version of SQL Server that you're trying to install does comprise the ready to enable TLS 1.ii support, y'all receive the following error message:A connection was successfully established with the server, but and then an fault occurred during the pre-login handshake. (provider: Named Pipes Provider, error: 0 - No procedure is on the other end of the piping.)In both of these situations, the installation fails.Please refer KB3135769 for the workaround for the issue.
Issue 6: Intermittent Service Termination
The following SQL Server database engine versions are affected by the intermittent service termination issue that is reported in KB3146034 . For customers to protect themselves from the service termination issue, nosotros recommend that they install the TLS ane.2 updates for Microsoft SQL Server that are mentioned in this article if their SQL Server version is listed in the following tabular array.
| SQL Server release | Affected version |
| SQL Server 2008 R2 SP3 (x86 and x64) | ten.50.6537.0 |
| SQL Server 2008 R2 SP2 GDR (IA-64 only) | x.50.4046.0 |
| SQL Server 2008 R2 SP2 (IA-64 only) | 10.50.4343.0 |
| SQL Server 2008 SP4 (x86 and x64) | 10.0.6543.0 |
| SQL Server 2008 SP3 GDR (IA-64 only) | 10.0.5544.0 |
| SQL Server 2008 SP3 (IA-64 only) | 10.0.5894.0 |
Issue vii: Database Mail does not work
Database Mail does not work with TLS 1.2
Database Postal service fails with the post-obit errors:
Agent Log:
Microsoft.SqlServer.Management.SqlIMail.Server.Common.BaseException:
Post configuration information could non exist read from the database.
….
….
Unable to kickoff post session.
See the section " Additional fixes needed for SQL Server to use TLS 1.2 " in KB3135244 .
Result 8: SQL Server service does not start
You get the following error later on disabling all other protocols except TLS one.2 on the server while trying to start the SQL Server database engine service.
Error: 17182, Severity: 16, State: 1.
TDSSNIClient initialization failed with error 0x139f, status code 0x1. Reason: Initialization failed with an infrastructure error. Bank check for previous errors. The grouping or resources is not in the right country to perform the requested operation.
Could not kickoff the network library because of an internal mistake in the network library. To make up one's mind the crusade, review the errors immediately preceding this ane in the error log.
Error: 17120, Severity: 16, State: 1.
SQL Server could not spawn FRunCM thread. Check the SQL Server fault log and the Windows event logs for data about possible related issues.
The above errors are reported because the SQL Server customer driver fixes were not applied on the server. Please refer KB3135244 and use the applicable client driver fixes on the server.
A recording of the TLS i.2 session delivered the Security Virtual Chapter for Pass is bachelor below.
Source: https://techcommunity.microsoft.com/t5/sql-server-blog/tls-1-2-support-for-sql-server-2008-2008-r2-2012-and-2014/ba-p/384613
Posted by: jacksontopoicusin1947.blogspot.com

0 Response to "How To Enable Tls 1.2 On Windows Server 2008 R2"
Post a Comment